Considering how often many of us fly on commercial airlines, the idea that a hacker could somehow interfere with the plane is a very scary thought. It doesn't help to learn that at Defcon, a researcher found that the Automatic Dependent Surveillance Broadcast (ADS-B), transmissions that planes use to communicate with airport towers are both unencrypted and unauthenticated.
So, not only would it be fairly easy to transmit fake signals to and from planes in the air, but the pilots and air traffic controllers would have no way of knowing if it was real or not.

Hacking into an airline's ADS-B protocol isn't theoretical either, it's actually fairly easy to do for anyone with a bit of know-how. A $20 USB TV-tuner can be turned into a software-defined radio that can receive ADS-B signals. Even less tech-savvy individuals can easily pick up a pre-built ADS-B compatible radio for well under $1,000.

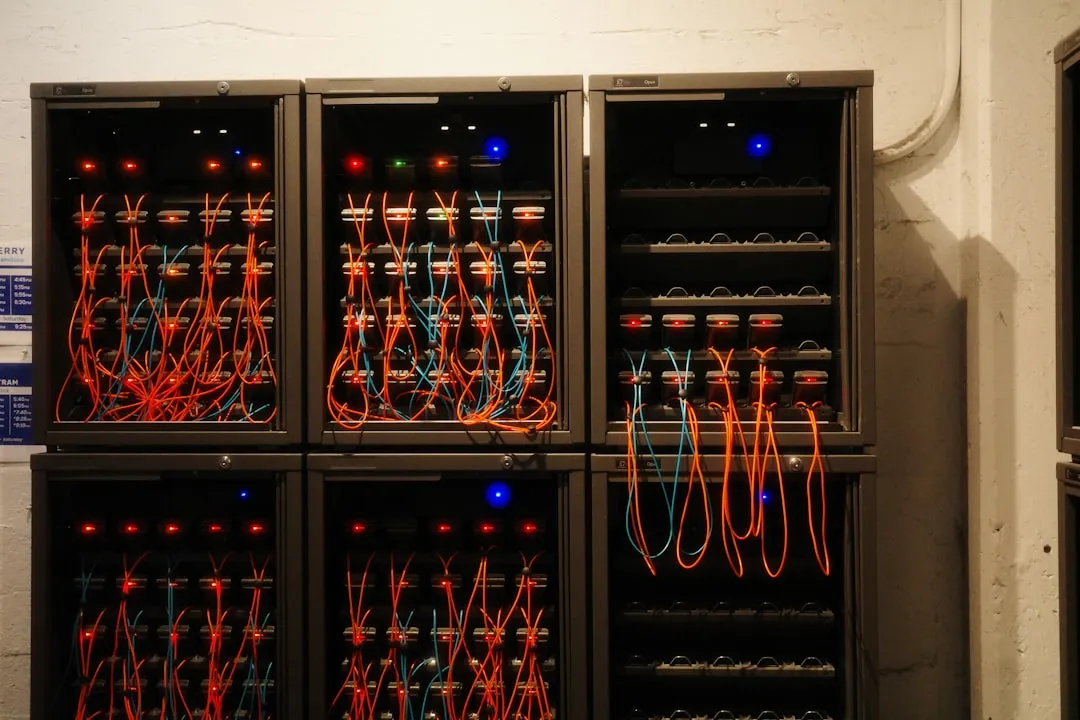
There are certainly benign uses, like tracking plane routes for fun perhaps, but the potential for harm is huge. A hacker could perform a real-life DoS attack by flooding an air traffic tower's system with fake signals from nonexistent planes. While air traffic controllers can manually check the transmissions against flight logs, there's no way to automatically see if a signal is authentic, meaning just a few thousand fake broadcasts could easily overwhelm the personnel.
Individuals could also hit pilots with fake reports of other aircraft in the vicinity, causing them to panic or change course to avoid hitting "ghost" planes. They could even make them crash into the ground during low-visibility scenarios. Even worse, some believe that technology similar to what was used by Iran to ground a military UAV could be utilized to bring down commercial aircraft.
Meanwhile, presenter at the Black Hat cybersecurity conference showed how it's possible to plot the route of Air Force One on an iPad, a method that he says could be exploited with only "modest technical skills and about $2,000 worth of electronics." And because aircraft registration numbers are public, a hacker could very well use the ADS-B vulnerabilities to track pretty much any private plane.
With hundreds of millions of dollars having already been spent setting up the ADS-B system, it seems unlikely that it will be dismantled anytime soon. Even worse, despite the inherent security issues, ADS-B will be mandatory by 2020. It's a pretty frightening thought, and we can only hope the shocking number of vulnerabilities get patched up before any harm can come of them. Until then, you can learn more by checking out the slides presented at Defcon.
Photos by Hack a Day, Jetbox, ScienceDaily, staybeautyful


















Comments
Be the first, drop a comment!